Space
The intelligent code collaboration platform
Space and SpaceCode will be discontinued on June 1, 2025. Learn more → →
Branch and Push Restrictions for Git Repositories in Space
Teams using Git repositories in Space can setup rules to limit what contributors can do, or to enforce certain standards. Branch restrictions let us restrict who can create and delete branches, and who can (force) push to a branch. With push restrictions, we can verify committers, limit file size and file types.
Let’s look at a few examples!
Branch Restrictions Prevent Changes that are Hard to Undo
In Space, we can make use of branch restrictions to prevent certain changes to a repository, typically those that are hard to undo. We can enforce restrictions on everyone in the team, and specific roles or members. And because there’s an exception to every rule, Space also lets us set those.
An example use case for branch restrictions would be to prevent force push to the master branch. Since a forced push always overwrites the remote, having someone force push may result in newer code changes being lost. Even if the person who’s force pushing took precautions by updating their local version of the repository, there’s still the hassle of every team member having to update their local repo.
From the repository settings, we can Edit Branch Restrictions, and create a rule for one or more branches.
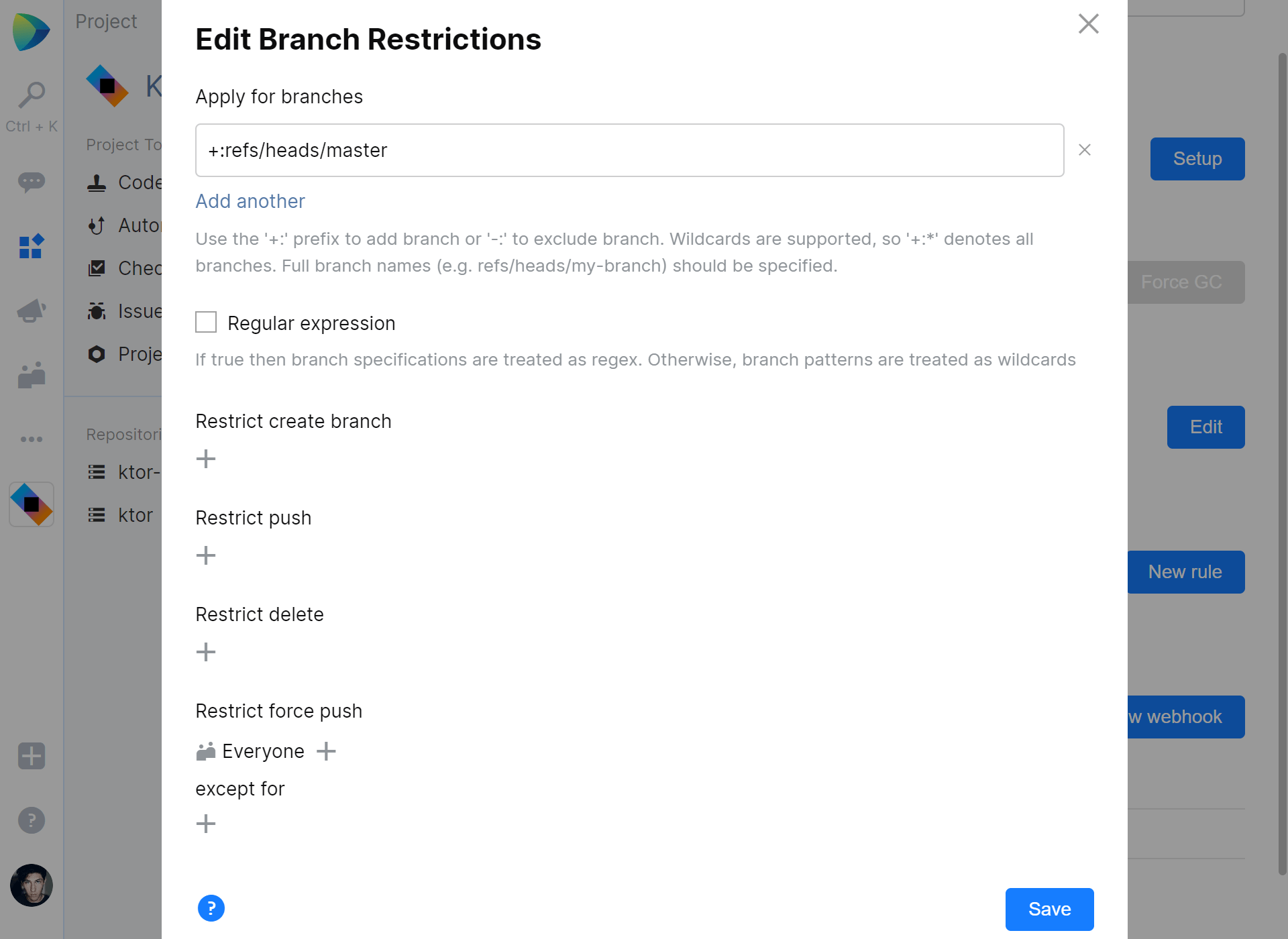
We can use the +: prefix to include a branch, or -: to exclude it. Branch specifications need the full branch name, so for the master branch we woud have to specify +:refs/heads/master. Regular expressions can be used here as well, if needed.
Now, what could we do here… Branch restriction setup will depend on the workflow the team will be using.
We can configure our trunk (or master branch) in such a way that nobody can push to it directly, except for certain project roles or team members. This would encourage the use of branches and merge requests to review code, allowing only a few folks to merge those into master. Several rules can be added and combined, with different settings per branch or set of branches.
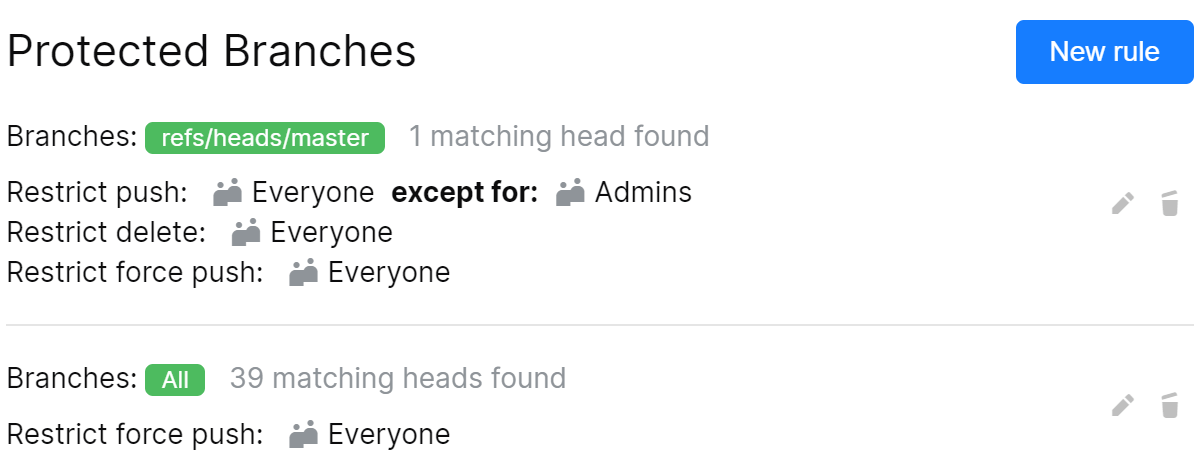
Note: protecting a branch from pushing changes applies to direct pushes from a developer machine, and to merge requests. Restricting push to everyone effectively restricts any push, by anyone. Make sure to set exceptions for certain roles or team members.
Push Restrictions help with Commit Best Practices
Next to branch restrictions, Space also lets us specify push restrictions for Git repositories. These can be used to enforce best practices, such as limiting file size, or making sure the committer matches the user who’s pushing to the repository.
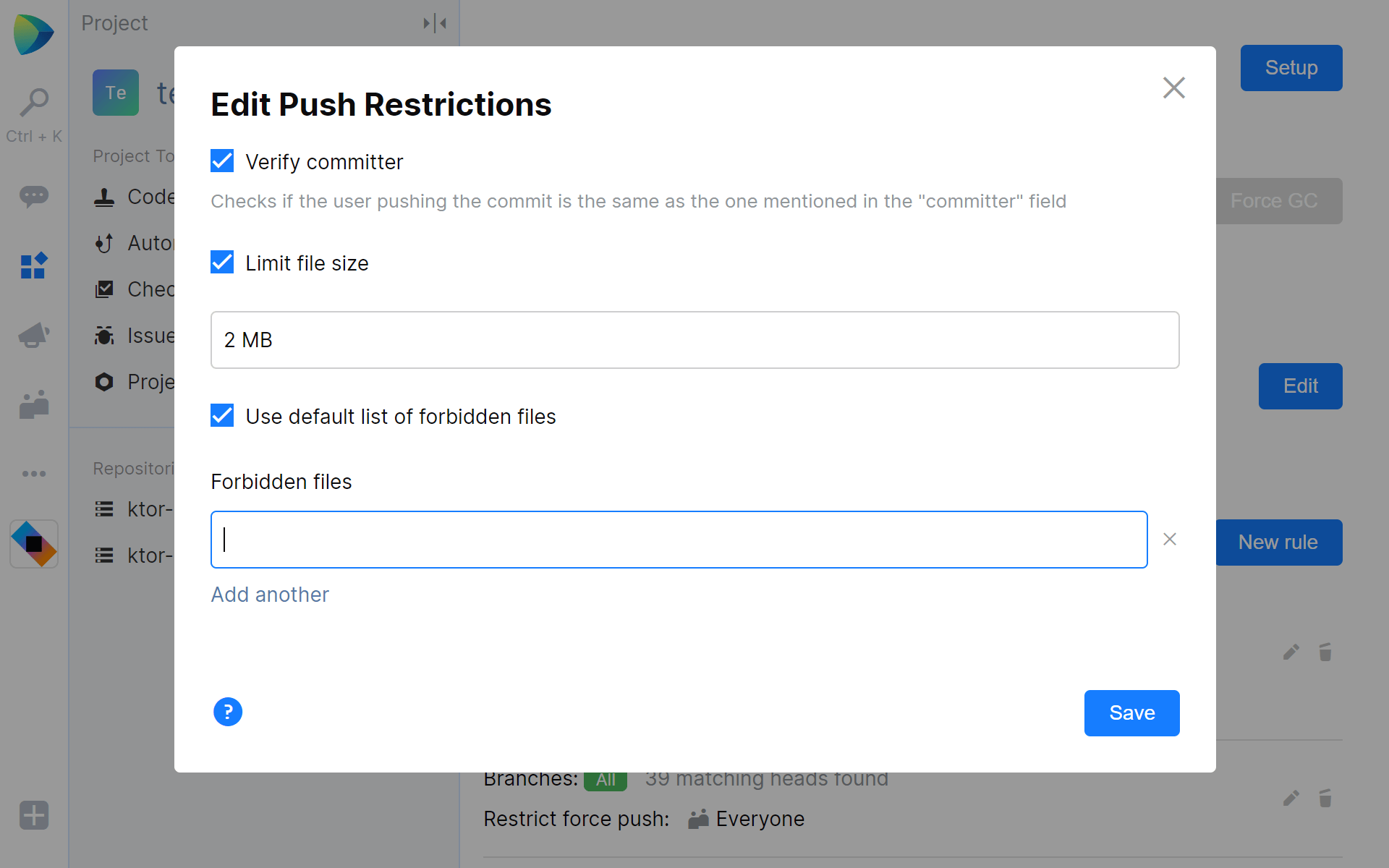
Verifying the committer is especially useful when folks on the team contribute to multiple code bases. For example, when they have their Git e-mail configured as a personal e-mail address, Space can reject their commits unless they use a company e-mail address.
Tip: the commit e-mail address in Git can be overridden per repository. From a local repo, run the following to specify the commit e-mail address for that repository:
git config user.email "email.address@example.com"
Developers spend a lot of time working with Git. Using branch and push restrictions in Space can help improve their productivity by preventing accidental or unwanted changes, and by assisting in using best practices for commits.
Give JetBrains Space EAP a try and let us know what you think!






