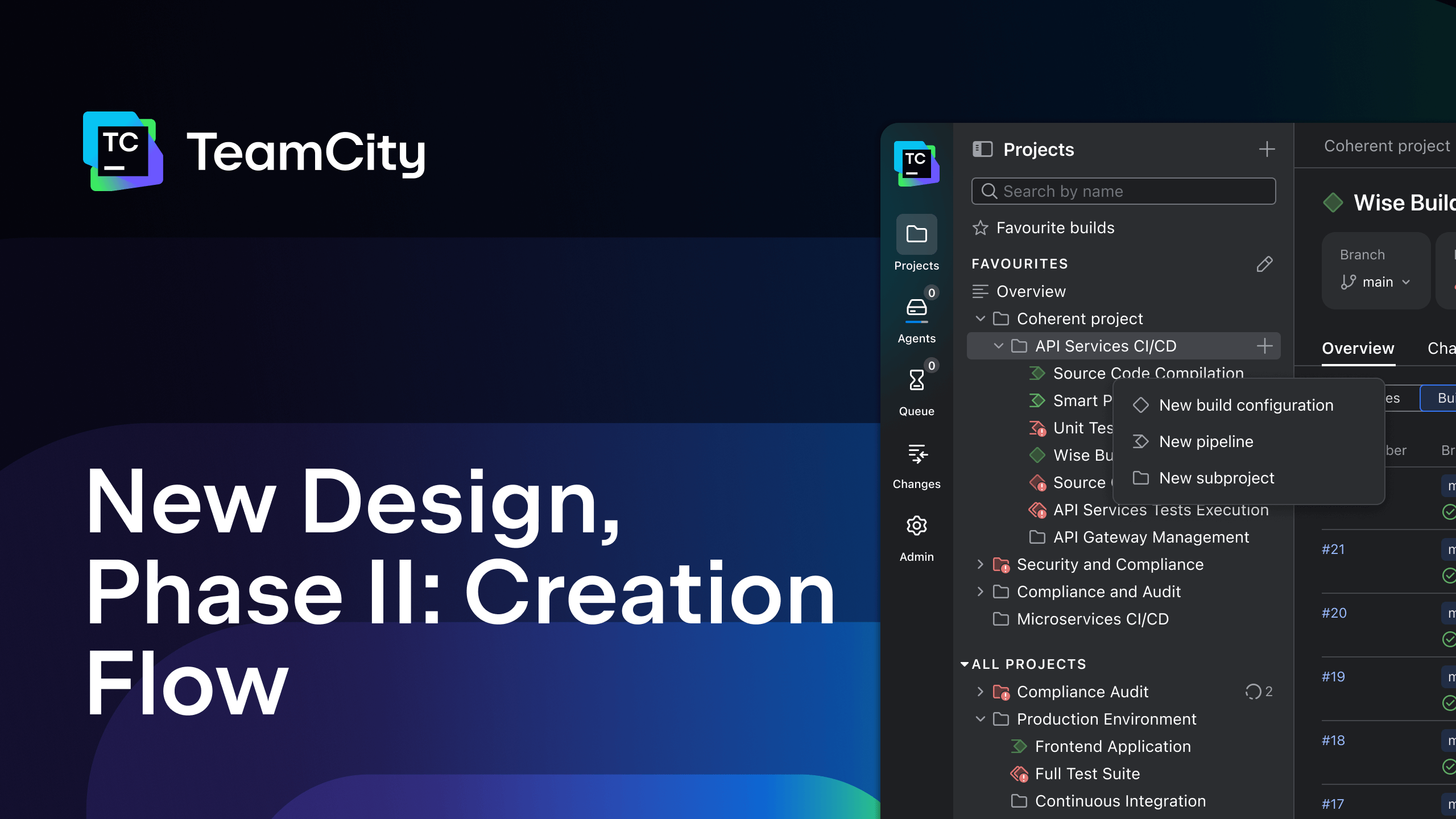
TeamCity
Powerful CI/CD for DevOps-centric teams
 Promo image
Promo image
News
Release
What’s New in TeamCity 2025.11: AI Assistant, New Pipeline Features, Enhanced Server Encryption Settings, and More
TeamCity 2025.11 introduces new build steps for pipelines, enhanced encryption settings, and a refreshed experience that makes powerful CI/CD workflows easier to create and manage. Here’s what’s new …