TeamCity
Powerful CI/CD for DevOps-centric teams
Enforced Settings with Templates
Enforcing some rules in a project might be quite useful to keep the things in order. For instance, enforce agent side checkout everywhere, or make sure that all build configurations have some strict execution timeout, or enable build files cleanup (Swabra) for all the builds.
Starting with 2018.1, TeamCity provides the ability to enforce settings for all of the build configurations in a project hierarchy.
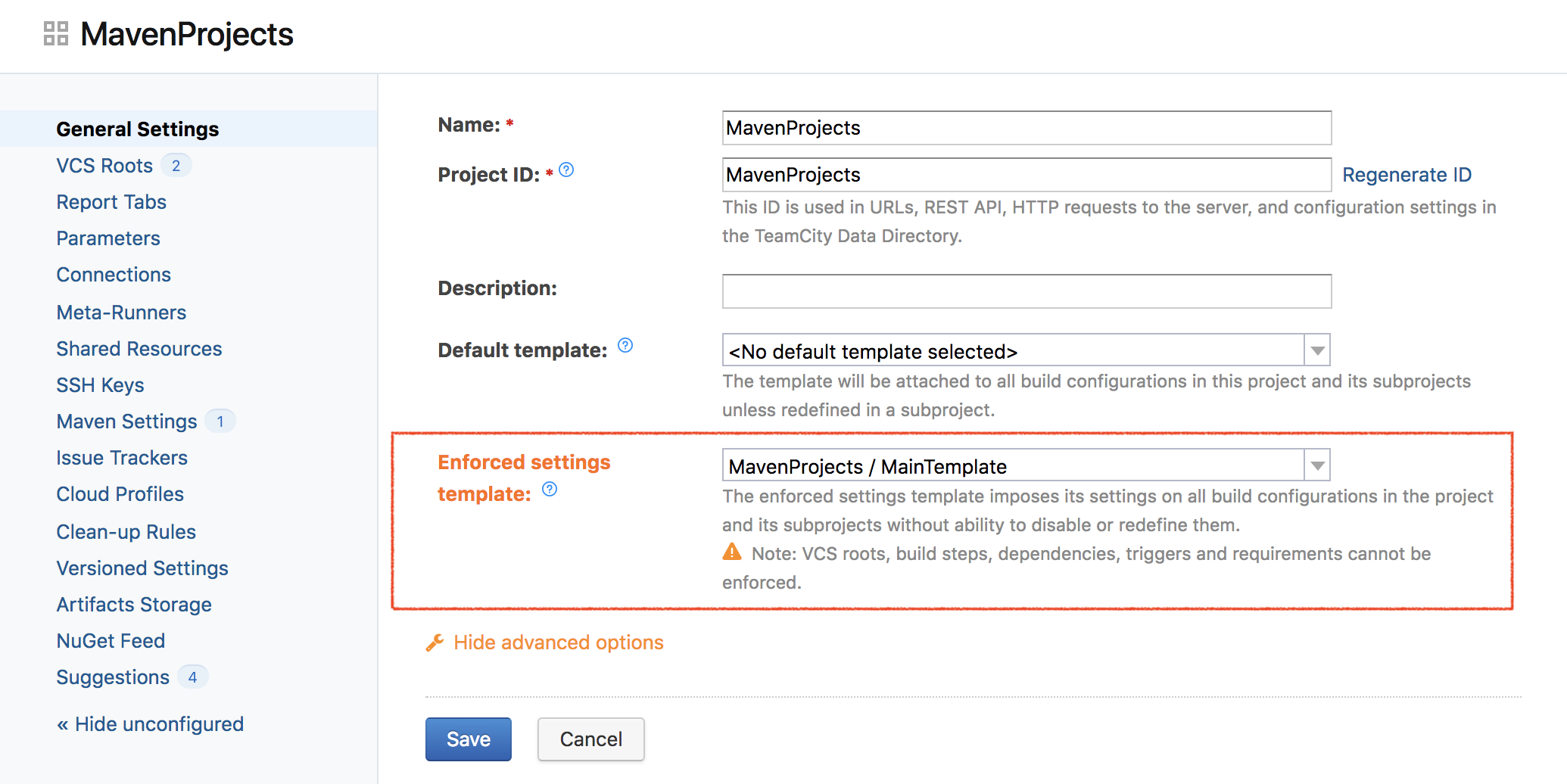
To enforce some settings in the project hierarchy, a template with these settings must be created. After that, a system administrator can set this template as the enforced settings template in the project:
To some extent, the enforced settings template works similarly to the default template – i.e., build configurations inherit all of its settings in the project hierarchy. The difference is that these inherited settings cannot be disabled or overridden anyhow.
In addition to that, only system administrator can associate a project with a specific enforced settings template, project administrator permissions are not sufficient. So it makes sense to store the enforcement template in a place that is only editable by a system administrator, for instance – in a Root Project.
On the other hand, the template itself can be edited by a project administrator who can administer the project where the template is defined. If the enforced settings template is specified in a project and another template is assigned as the enforced settings in a subproject, the subproject’s template has the higher priority.
Currently it is not possible to enforce VCS roots, build steps, triggers, dependencies and requirements. Let us know if you see valid use cases when this would be useful.





